- May 11, 2026
- Posted by: admin
- Category: BitCoin, Blockchain, Cryptocurrency, Investments
Crypto projects with more than $3 billion in total value locked have migrated their cross-chain infrastructure to Chainlink’s Cross-Chain Interoperability Protocol (CCIP) following a $292 million exploit at KelpDAO, which heightened scrutiny of bridge security across decentralized finance.
Chainlink confirmed the migration wave, saying four protocols, including KelpDAO, Solv Protocol, Re, and Tydro, had begun decommissioning legacy oracles and bridge systems in favor of CCIP.
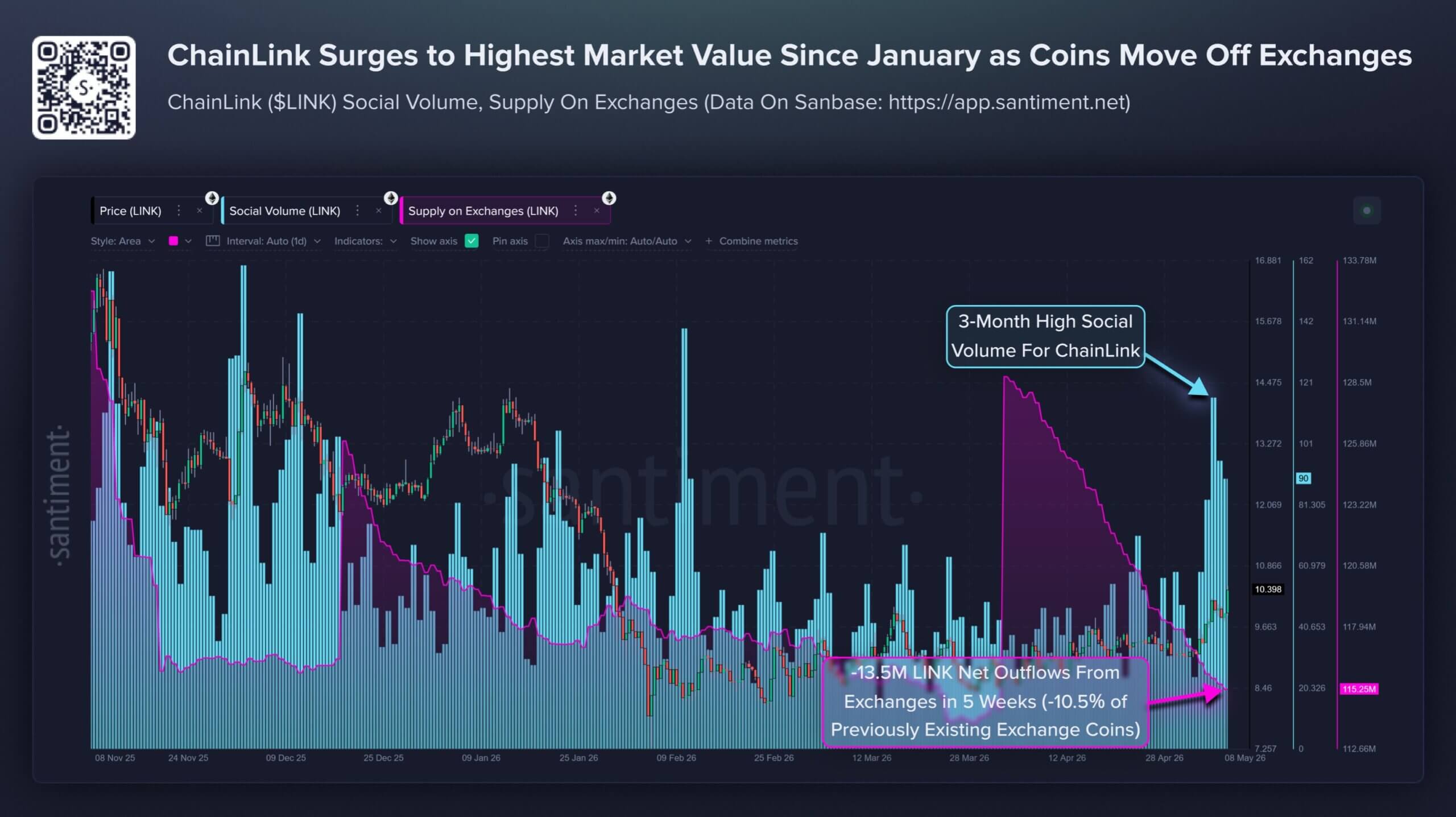
The shift has also fed into LINK’s market performance. CryptoSlate data shows the token rose 15% to $10.52, its highest level since January, as traders responded to the acceleration in CCIP adoption.
Blockchain analytics firm Santiment said the rally came alongside a tightening in LINK’s available supply on exchanges. According to the firm, LINK’s exchange reserves fell by 13.5 million LINK over five weeks, representing more than 10.5% of the exchange-held supply recorded in early April.
The price move reflects a broader reassessment of Chainlink’s role in crypto infrastructure. After years of being known primarily for price feeds and oracle services, the network is now becoming a direct beneficiary of DeFi’s search for safer cross-chain rails.
Why are DeFi protocols embracing Chainlink’s CCIP?
Cross-chain bridges allow tokens, NFTs, and data to move between otherwise separate blockchain networks. This means these platforms let users shift liquidity between ecosystems, such as moving assets from Ethereum to Solana, without relying on a centralized exchange.
That function has become essential as DeFi has spread across multiple blockchains. Lending markets, staking tokens, stablecoins, and tokenized assets increasingly depend on infrastructure that can move value between networks without fragmenting liquidity or locking users into a single chain.
However, bridges have also become one of crypto’s most frequently attacked pieces of infrastructure. This is because they often rely on complex verification systems and hold large pools of locked assets, making them attractive targets for hackers.
Chainalysis has described cross-chain bridges as one of the blockchain industry’s major security risks. As of 2022, more than $2 billion had been stolen across 13 bridge hacks, with North Korean-linked groups among the most active attackers.
That history has pushed DeFi protocols toward infrastructure that can offer more standardized security controls. Chainlink’s CCIP, which launched on mainnet in July 2023, has become one of the main beneficiaries of that shift.
CCIP uses Chainlink’s decentralized oracle networks, the same infrastructure behind the data feeds that secure large parts of DeFi. Chainlink says those networks now include more than 2,000 decentralized oracle networks in production, securing over $110 billion in value and powering more than 70% of DeFi.
Unlike many traditional bridges, which can depend on a narrow set of validators or verification pathways, CCIP is designed to transmit both data and token value across chains through Chainlink’s oracle infrastructure.
That gives protocols a way to move assets while reducing reliance on bespoke bridge designs.
For protocols managing hundreds of millions of dollars in assets, cross-chain infrastructure is now being evaluated less as back-end plumbing and more as a core part of risk management.
LayerZero attempts to contain the fallout
Meanwhile, the migration wave has put LayerZero, the cross-chain platform previously used by KelpDAO, under pressure to explain its role in the $292 million breach.
LayerZero issued an apology on May 9, about three weeks after the April 18 breach. The company acknowledged that its post-exploit communication had fallen short and conceded that its security model allowed a high-value application to operate with insufficient safeguards.
LayerZero had initially maintained that its infrastructure worked as designed and that responsibility sat with the application configuration.
However, its more recent comments struck a different tone, acknowledging that it should have exercised stronger oversight over how its decentralized verifier network was used.
The company said it “made a mistake” by allowing its Decentralized Verifier Networks (DVNs) to function as the sole verifier for high-value cross-chain transactions without adequate guardrails.
It noted:
“We didn’t police what our DVN was securing, which created a risk we simply didn’t see. We own that.”
The admission goes to the heart of the dispute. LayerZero’s architecture gives application developers the flexibility to configure verification as they see fit. That customizability has long been part of the protocol’s appeal, particularly for teams seeking more control over their cross-chain security assumptions.
The KelpDAO exploit has exposed the weakness of that approach when teams operate with a too-narrow verification setup. If an application depends on a single verifier, a compromise in that layer can become a direct threat to user funds.
Meanwhile, LayerZero also disclosed a previously unreported incident from three years ago involving one of its multisig signers.
The company said the signer mistakenly used LayerZero hardware to conduct a personal trade. The signer was removed, wallets were rotated, and LayerZero later moved to a custom-built multisig framework.
The disclosure appeared intended to show that the protocol had addressed earlier internal security lapses. However, it also added another layer of scrutiny at a moment when clients were already reassessing their exposure.
LayerZero said the KelpDAO exploit affected only a single application, representing 0.14% of network applications and roughly 0.36% of total value on the protocol. It also said no other application was affected.
That defense leaves LayerZero with a narrow but difficult argument. The company is trying to show that the exploit was isolated while also admitting that the configuration should not have been allowed to secure so much value without stronger oversight.
Can LayerZero restore institutional confidence?
The central question now is whether LayerZero’s apology and technical explanation can slow the migration of protocols toward Chainlink.
Tom Wan, head of data at Entropy Advisors, questioned whether the damage to institutional confidence had already been done. He wrote
“Can an apology stop their clients from leaving to Chainlink, or is this just the beginning?”
LayerZero has tried to answer that concern with usage data. The company said more than $9 billion had moved through its infrastructure since the April attack, a figure meant to show that users and applications continue to rely on the protocol despite the KelpDAO incident.
Wan also noted that several major assets, including USDe, WBTC, and weETH, remain active on LayerZero.
That continued usage suggests the protocol has not suffered a full loss of confidence, even as several prominent projects shift parts of their cross-chain stack elsewhere.
LayerZero also retains defenders who argue that the protocol’s flexibility remains its core advantage.
In that view, customizability is not a flaw by itself. The risk arises when application teams fail to align their security configuration with the volume of capital flowing through their systems.
Lorenzo Romagnoli, co-founder of USDT0, said LayerZero’s model requires asset issuers to take security seriously from the start. USDT0, the largest asset on the LayerZero network, has moved $4 billion across chains without incident.
Romagnoli said:
“LayerZero is the golden standard for cross-chain interoperability because of its high level of customizability. Unfortunately, this means application owners need to invest serious resources to match the security standard that the capital moving through our rails demands.”
Romagnoli said USDT0 operates its own proprietary veto-powered DVN, with invariance checks tailored to its specific risk profile. He argued that the protocol remained unaffected because it treated security as part of the product, rather than a feature inherited automatically from the underlying rails.
That defense captures the wider debate now facing cross-chain infrastructure. Protocols want flexibility, but they also need defaults and guardrails strong enough to protect large pools of user capital. The KelpDAO exploit has made that trade-off harder to ignore.
For Chainlink, the migration wave strengthens CCIP’s position as a security-focused cross-chain standard, as DeFi teams reassess vendor risk.
For LayerZero, the challenge is to demonstrate that its customizable model can meet institutional expectations without exposing high-value applications to weak configurations.
The post Chainlink emerges as the unlikely $3B winner of KelpDAO exploit as DeFi projects dump LayerZero appeared first on CryptoSlate.